Study Finds Construction Cranes Vulnerable to Hacking
Radio-controlled tower and mobile cranes easily compromised by researchers

Researchers at computer security firm Trend Micro found that over-the-air radio signals for remotely operated cranes on construction jobsites and industrial settings were unencrypted and vulnerable to hijacking.
Image Courtesy of Trend Micro
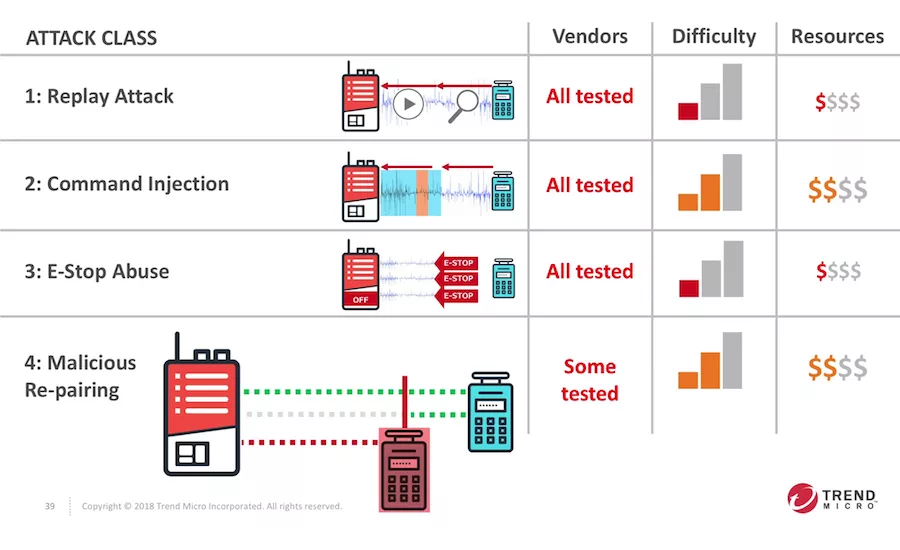
All 17 of the RF remote-control manufacturers tested were found to be vulnerable to the most basic hacks, some of which were fairly unsophisticated and required only a basic knowledge of electronic engineering.
Image Courtesy of Trend Micro
When securing a jobsite against malicious hackers, most go to protect computer files, and few look up and worry about the tower cranes. But many cranes—whether tower, mobile or industrial—can be remotely run via radio wireless controllers, a useful feature for when operators need a clearer view of the load from the ground. Unfortunately, these wireless signals are vulnerable to hijacking, according to a study released earlier this year by security research firm Trend Micro. It found that the radio signals these crane controllers use are not encrypted over the air in any way, and can be easily intercepted and spoofed using off-the-shelf equipment and a basic knowledge of electronics and radio engineering.
“In other operational and industrial technology, there are some security measures,” says Greg Young, vice president of cybersecurity at Trend Micro. “In this case, we didn’t have to find vulnerabilities. There was no need to pick the lock on the door, the door was open—no encryption, no proprietary protocols.”
|
Related Article |
Trend Micro researchers tested 17 brands of wireless controllers at sites in the U.S., Europe and China on real cranes on jobsites and industrial settings. All of the vendors’ radio remote controls were found to be susceptible to attacks.
Typically, a remote control is paired to a crane, and radio signals are used to send and acknowledge commands. What researchers found was their antennae could sniff out and isolate the crane’s radio traffic simply by comparing the signals to the crane’s actions. They then guessed that the radios and microcontrollers used standard sub-gigahertz frequencies, and wrote a program to monitor and record traffic and reverse-engineer command signals.
“There was no need to pick the lock on the door, the door was open—no encryption, no proprietary protocols.”
– Greg Young, VP Of Cybersecurity, Trend Micro
All of the vendors tested were susceptible to what’s called a “replay” attack, where an attacker just replays recorded radio signals to make the crane perform the same action as before. This is the simplest form of attack, requiring only high-school knowledge of electronics, according to Young. All of the vendors also fell for the slightly more sophisticated “emergency stop” attack, where analyzer software isolates the crane’s shut-off command and transmits it repeatedly, as well as actual command injection, where reverse-engineered commands are sent to the crane, overriding the actual remote. None of the attacks required physical access to the crane or the real controller.
The findings were first published in January 2019, and according to Trend Micro, researchers contacted vendors ahead of time to explain the vulnerabilities in their systems. But Trend Micro says few have taken any action since to close security holes on older, outdated models. “Once these things are deployed, they tend to be in service a very long time,” says Young. “ There is very little drive to replace them. Even if there is enthusiasm among the vendors, it is going to take a little while to address this problem.”
Trend Micro researchers present their findings on crane hacking at the S4x19 conference in Jan. 2019.
There were some bright spots. While sub-gigahertz-range radio-based controls are outdated and vulnerable, some manufacturers are moving toward Bluetooth and other widely used radio technologies with more robust security. A newer Liebherr crane remote examined by Trend Micro uses standard Bluetooth, which is not subject to the same vulnerabilities as the equipment tested in the study. As manufacturers move to 2.4-GHz standards like Bluetooth to reduce interference and improve reliability, better security may be a side effect. “[Construction] equipment vendors are enthusiastic for things to become more connected, not just for diagnostics but for greater remote control and autonomy,” Young says. “They are keen on security, but it’s also very new for them. They are focusing on new technology, [but] the legacy of in-service technology will be around for 10 to 20 years.”
Looking for quick answers on construction and engineering topics?
Try Ask ENR, our new smart AI search tool.
Ask ENR →



